How can we continue to build cybersecurity into systems in a way that ensures future compliance? This is a hot topic featured on the AutoSens Brussels agenda in September, and one our Lead Sponsor onsemi are tackling head on. In this article, Radhika Arora, Sr. Director, Product Management, explores the upcoming regulations and breaks down the different types of cybersecurity threats.
“Just because you are paranoid doesn’t mean they aren’t after you” – Joseph Heller, author of Catch-22. What was true in 1961 when the book was first published remains just as true today. The basic building blocks remain the same – there is an army of technically adept folks hacking into vehicles for reasons ranging from “just because I can” to extortion and terrorism.
We have been lucky enough to witness a complete shift in the automobile industry where innovation has forced vehicles to turn into veritable computing platforms and data-sharing powerhouses. The automotive industry is at this inflection point with electrification, ride-sharing and active safety metamorphosizing the world as we know it today. These innovations come with significant advantages. Autonomous driving coupled with electrification will make for a better, greener environment. Part of the vision for autonomous driving is to increase the utilization of vehicles significantly. Typical cars that are only being driven for an hour a day, will be driven for almost 20 hours a day. Thus, instead of sitting idle in a parking lot all day long, automobiles will ferry around a lot more passengers and goods throughout the day. This will change our cramped cities by converting most of the parking lots in prime locations, to green or multi-use community spaces leading to a healthier life for all.
This automobile of the future, which will drive around all day with minimal or no human supervision, will by most accounts have 100s of microcomputers with 100s millions of lines of code connected with 10s of sensors and actuators; all of which will provide an open invitation for potential cyber attacks. These cyber threats can either come from physical or remote access. As vehicle connectivity increases in the future, so will the threat vectors for remote attacks.
The industry today clearly understands cybersecurity needs to be built into all electronic systems and components. Threat vectors now have a wider range with a large attack surface with security arguably not keeping pace with change. Industry reports suggest that black hat hackers are more common now in the automotive sector than white hats, with greater than half the attacks being carried out by those with nefarious motives. According to a recent report by Upstream Security, there was a staggering 99% increase in automotive cybersecurity incidents. The industry has responded with releasing a draft of two regulations that will influence all aspects of automotive cybersecurity and associated software & hardware solutions. A key tenet of these cybersecurity standards and regulations will dictate that each vehicle must be secured throughout its entire lifecycle from development to production, through all stages of the customer use phase. The onus will be on the OEMs to architect their systems and define their supply chains to incorporate multi-layered cybersecurity solutions to protect against a multi-faceted attack.
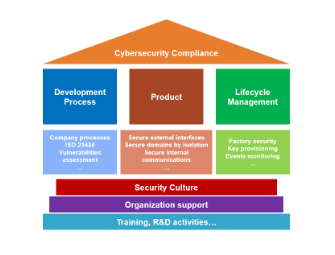
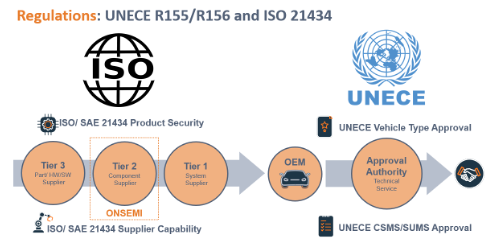
The World Forum for the harmonization of vehicle regulations (WP.29) consists of two components: R155 cybersecurity management system (CSMS) and R156 software update management system (SUMS). CSMS is focused on implementing a high level of cybersecurity analysis, while SUMS is dedicated to safeguarding software updates during the vehicle lifecycle.
ISO/SAE 21434 is focused on implementing WP.29 CSMS requirements at the beginning of the system design process and enabling OEMs and suppliers to demonstrate engineering rigor and due diligence to delivering cybersecurity systems.
For onsemi, being a leader in providing advanced safety solutions to the industry, providing safe and secure sensors is part of our DNA. It started with functional safety which we have been focusing on for many years in accordance with ISO 26262 and have learned the importance of incorporating it at the very onset of design. During development, we inject faults into every node of our image sensors and observe errors never predicted or expected before. Understanding these failures means we have designed all our hardware cores to be able to detect faults and report them to the processor at every frame. This enables us not only to find failures but do so with speed and accuracy. This results in stopping the failure from propagating to create a dangerous situation. This is part of our responsible engineering culture where we don’t throw faults over the fence to the processor and expect them to address it with software. We have extended the same rigor to adding cybersecurity to prevent hacks or any human interference that would compromise safety.
We break down the cybersecurity threats into 4 major buckets – counterfeiting, tampering, bypassing, and eavesdropping:
Counterfeiting is the simplest attack point where vehicle cameras are replaced with unauthentic components. This could have a direct impact on safety systems with subpar sensor outputs being fed to a processor or worse still inaccurate data with malicious intent leading to a collapse of the safety systems.
Tampering is another type of threat vector that involves altering the video data by adding, removing or modifying objects in view. This has a direct impact on decision making, as actions are taken based on inaccurate data that is being fed to the system.
Bypassing is the third identified cyber attack. This threat could be in the form of bypassing an image sensor entirely that can render the vehicle blind, preventing the detection of potential hazards. An image sensor provides the image processor with raw video data, which is used to extract critical information about front-facing obstacles so that the car can respond appropriately. For example, the system receiving raw video data from the sensor can detect an approaching vehicle and decide to use the brakes or steer the car away from the hazard (whichever is the safest action). If the image sensor has been bypassed, the system is no longer receiving raw video data and it may not detect the approaching vehicle at all.
Finally eavesdropping (more applicable for in-cabin applications) refers to a scenario where captured video content is used for tracking purposes with malicious intent.
onsemi has implemented cybersecurity features in selected ADAS image sensors since 2018, and these sensors are on track to be cybersecurity compliant by 2024. The authentication feature allows our sensors to prove to the host that they are genuine. This is accomplished by supporting a range of key/certificate models. To ensure video stream authentication, sensors will provide a row of embedded data containing message authentication codes (MACs) for the entire frame. This confirms that a video data stream has not been tampered with between the sensor and the host. Finally, sensor control and configuration data are protected against tampering with specific key registers using MACs. In summary secure initialization, video authentication, control channel data encryption, and multi-party key management are the key building blocks of onsemi cybersecurity solutions.
Cybersecurity is no longer an optional add-on feature, but an essential aspect of ensuring the safety and reliability of vehicles. By recognizing the importance of cybersecurity, the automotive industry can proactively address the risks from a growing set of threat vectors. The newly released cybersecurity standard will ensure a consistent and comprehensive approach to protecting vehicles. Having driven expansive innovation, we as a society need to come together and through informed sharing among industry stakeholders drive toward a safer and more secure world. A world where the vast potential and vision of the future of transportation can be truly fulfilled.
Are you ready to learn more about how cybersecurity will be incorporated into the automobile of the future? Get your AutoSens Brussels pass and check out these sessions from onsemi…
WHY AUTOMOTIVE IMAGE SENSORS NEED TO BE CYBER-SECURE
- 2:15pm CET
- Wednesday 20th September
- Mahy Room

Ludovic Rota
Product Marketing Manager
onsemi
IMAGE SENSORS FOR SAFER ROADS
- 10:15am CET
- Wednesday 20th September
- Mezzanine Stage
Sergey Velichko
Senior Manager, ASD Technology and Product Strategy
onsemi